Tag: DNS Security

Unveiling the Mysteries of DNS Records: The Backbone of the Internet
In the heart of the vast digital landscape lies a system as foundational as the...
The Future of DNS: New Technologies and Trends
In the vast landscape of the digital world, the Domain Name System (DNS) serves as...

Overview of Tools for Testing and Diagnosing DNS
When it comes to the world of networking, DNS (Domain Name System) is akin to...

How DNS Affects Web Application Security: A Comprehensive Guide
In an age where our digital presence is akin to our cultural identity, the importance...
How to Protect Your DNS Server from DDoS Attacks
In the vast digital landscape, where data flows like the great rivers of Mongolia, our...

Using DNS for Content Filtering: A Comprehensive Guide
In the ever-evolving landscape of internet security and content management, the Domain Name System (DNS)...
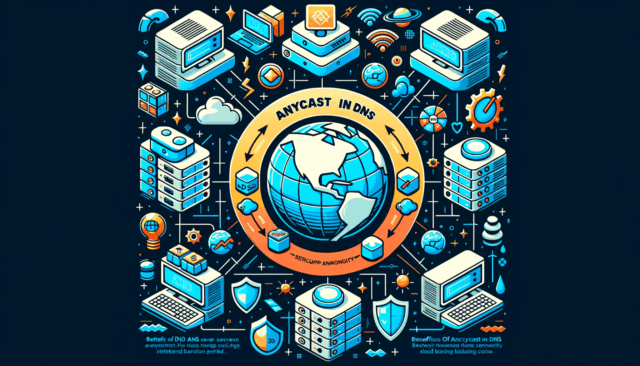
Using Anycast in DNS: Advantages and Setup
Imagine you’re at a bustling café, and you’ve just ordered the most complicated coffee known...

DNSSEC: What It Is and Why It’s Needed
In the vast digital steppes of the internet, where information flows like the mighty rivers...
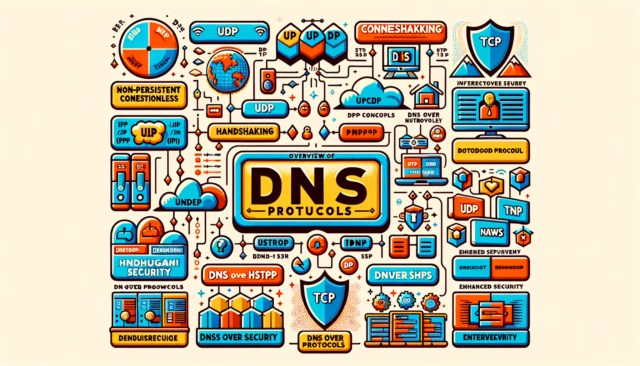
Overview of DNS Protocols: UDP, TCP, DNS over HTTPS, and Others
In the vast digital landscape, where every click and connection is a dance of data,...

Implementing DNS-Based Compliance Reporting: A Comprehensive Guide
In the ever-evolving landscape of digital technology, maintaining compliance with various regulations is paramount for...

The Role of DNS in Financial Services Security
The Role of DNS in Financial Services Security: A Bhutanese Tale of Digital Vigilance In...

Implementing DNS-Based User Authentication: A Comprehensive Guide
In the ever-evolving landscape of cybersecurity, user authentication has become a cornerstone of protecting sensitive...
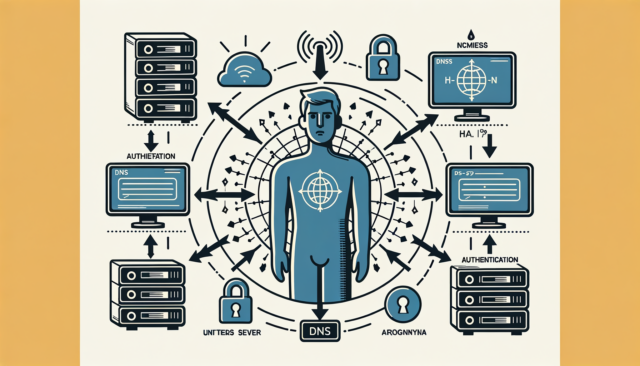
Implementing DNS-Based User Authentication: A Comprehensive Guide
In the realm of digital security, DNS isn’t just the phonebook of the internet; it’s...

Implementing DNS-Based User Authentication
Implementing DNS-Based User Authentication: A Journey Through the Kingdom of Networks In the serene valleys...

Implementing DNS-Based Application Layer Security
Implementing DNS-Based Application Layer Security: A Guide for the Savvy Digital Explorer Hey there, fellow...

Implementing DNS-Based Data Exfiltration Prevention
When it comes to the intricate web of internet protocols, the Domain Name System (DNS)...

Harnessing the Power of DNS to Fortify API Security
In the bustling bazaars of Tehran, where vibrant tapestries hang alongside fragrant spices, I often...

How DNS Supports Blockchain-Based Applications
Hey there, tech trailblazers and digital adventurers! Today, we’re diving into the electrifying world of...

The Role of DNS in Mobile App Security
Hey there, digital explorers! Today, we’re diving into the world of mobile app security, and...

Implementing DNS-Based Fraud Detection
Implementing DNS-Based Fraud Detection: A Blend of Tradition and Technology In the vast steppe of...

Implementing DNS-Based Security Policies
Implementing DNS-Based Security Policies: A Bhutanese Journey into the Digital Realm In the lush valleys...

How DNS Supports Hybrid IT Environments: Bridging the Gap
In the ever-evolving landscape of IT infrastructure, the term “Hybrid IT” has become a cornerstone...

The Role of DNS in Cyber Threat Intelligence: Unveiling the Hidden World
In the tranquil valleys of Bhutan, where stories of yore are passed down like the...

Using DNS for Secure Remote Access Solutions
In the ever-evolving landscape of cybersecurity, ensuring secure remote access has become a paramount concern...

DNS and Quantum Computing: Future Implications
DNS and Quantum Computing: Future Implications In the bustling bazaars of Tehran, where the vibrant...

Using DNS to Support Multi-Factor Authentication (MFA)
Harnessing the Power of DNS to Fortify Multi-Factor Authentication (MFA): A Modern Approach with Ancient...

DNS as a Service (DNSaaS): Benefits and Providers
In the digital age, where the virtual realm seamlessly intertwines with our daily lives, the...

The Role of DNS in Secure Software Development Lifecycle (SDLC)
In the vast, interconnected realm of software development, the Domain Name System (DNS) often plays...

Implementing DNS-Based Access Controls: A Comprehensive Guide
Imagine a bustling medieval kingdom where the castle gates are constantly under siege by mischief-makers...

DNS and Artificial Intelligence: Emerging Trends
Imagine you’re trying to invite your friend over for dinner, but instead of using their...