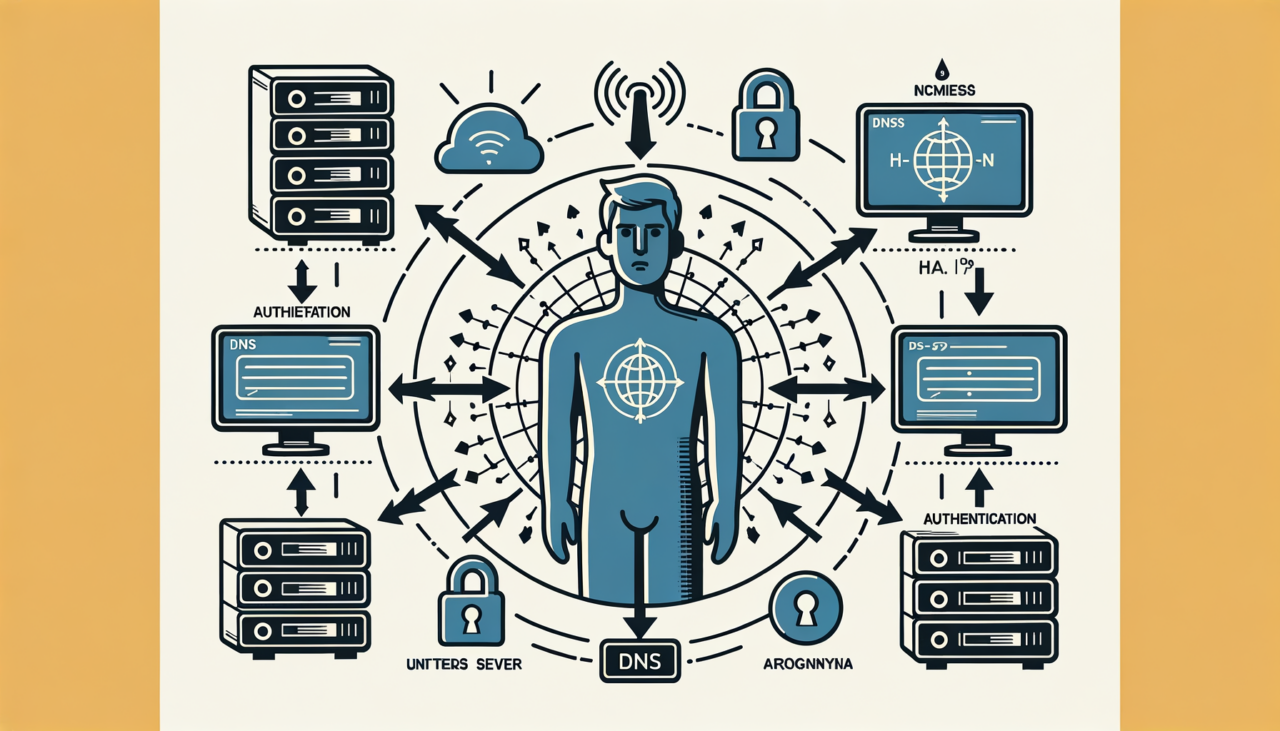
In the realm of digital security, DNS isn’t just the phonebook of the internet; it’s evolving into a sophisticated tool for user authentication. As we delve into the intricacies of DNS-based user authentication, we’ll explore how this technology can enhance security protocols, drawing from both my vast career experience and emerging trends in cybersecurity.
Understanding DNS and Its Role in Authentication
Before we dive into the implementation, let’s take a step back and understand the critical role DNS plays in internet communications. DNS, or Domain Name System, translates human-readable domain names into IP addresses, facilitating seamless connectivity across the internet. Imagine DNS as the digital equivalent of a reliable postman, ensuring that your requests and data packets reach the right address.
Now, you might wonder, how does this relate to user authentication? Traditionally, user authentication relies on credentials like usernames and passwords. However, these methods are susceptible to breaches. DNS-based authentication, on the other hand, leverages the inherent security features of DNS to authenticate users, providing an additional layer of protection.
DNS-Based User Authentication: The Why and How
Why Opt for DNS-Based Authentication?
- Enhanced Security: By using DNS queries and responses as part of the authentication process, you can reduce the risk of credential theft.
- Scalability: DNS infrastructure is inherently scalable, making it suitable for growing networks and user bases.
- Reduced Latency: Since DNS operates at a fundamental level of internet connectivity, it can offer faster authentication processes.
How Does DNS-Based Authentication Work?
At its core, DNS-based authentication involves using DNS records to verify user identities. Here’s a step-by-step breakdown:
- User Initiation: The user initiates a connection request to a service.
- DNS Query: The service issues a DNS query to check for specific DNS records associated with the user’s domain.
- Verification: The DNS server responds with the necessary records, such as TXT or CNAME, which contain authentication tokens.
- Authentication Decision: The service verifies these records to authenticate the user.
To further illustrate this concept, let’s look at a simple DNS record setup for authentication:
; DNS Zone File for example.com
;
; Authentication TXT Record
auth._domainkey.example.com. IN TXT "v=DKIM1; p=MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQDl...=="
In this scenario, the DNS server checks for a TXT record under the subdomain auth._domainkey.example.com, which contains an authentication token.
Implementing DNS-Based Authentication: A Step-by-Step Guide
Now that we understand the “why” and the “how,” let’s dive into the actual implementation process.
Step 1: Set Up Your DNS Records
First, you’ll need to configure your DNS zone file to include the necessary records for authentication. This could involve creating TXT or CNAME records, depending on your authentication mechanism.
Example DNS Zone File
| Record Type | Name | Value |
|---|---|---|
| A | example.com | 192.0.2.1 |
| TXT | auth._domainkey.example.com | “v=DKIM1; p=MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQDl…==” |
Step 2: Develop the Authentication Logic
You’ll need to develop a backend system that can query DNS records and verify user identities based on the retrieved data.
Sample Code Snippet
Here’s a simple Python script to query DNS and verify a TXT record:
import dns.resolver
def verify_user(domain):
try:
answers = dns.resolver.resolve(f'auth._domainkey.{domain}', 'TXT')
for rdata in answers:
if "v=DKIM1" in rdata.to_text():
print("User authenticated successfully.")
return True
except dns.resolver.NoAnswer:
print("No authentication data found.")
except Exception as e:
print(f"An error occurred: {e}")
return False
# Example usage
verify_user('example.com')
Step 3: Integrate with Your Application
Finally, integrate this authentication logic into your application, ensuring that DNS queries and responses are handled securely and efficiently.
Real-World Applications and Anecdotes
Reflecting on my career, I recall an instance where a financial institution implemented DNS-based authentication to secure their transaction verification processes. By leveraging DNS, they achieved a significant reduction in fraudulent transactions, saving millions annually.
Another example is a multinational corporation that used DNS-based methods to authenticate remote employees securely, enhancing their work-from-home infrastructure during the pandemic.
Conclusion
DNS-based user authentication is more than a technical novelty; it is a robust solution to the evolving challenges of digital security. By leveraging DNS, organizations can enhance their security posture while maintaining scalability and efficiency. As you consider implementing this technology, remember that the key lies in understanding both the technical details and the practical applications.
Whether you’re a seasoned professional or a novice exploring new horizons, DNS-based authentication offers a promising avenue to explore. Embrace the power of DNS, and fortify your security infrastructure for the future.
By mastering DNS-based user authentication, you’re not just keeping up with the times; you’re staying ahead of the curve. So, why not start your journey today?
Comments (0)
There are no comments here yet, you can be the first!